The "Identity Surveillance Machine": Unpacking Allegations Against OpenAI, Persona, and the US Government
1. Introduction: Unpacking the "Identity Surveillance Machine" Claim
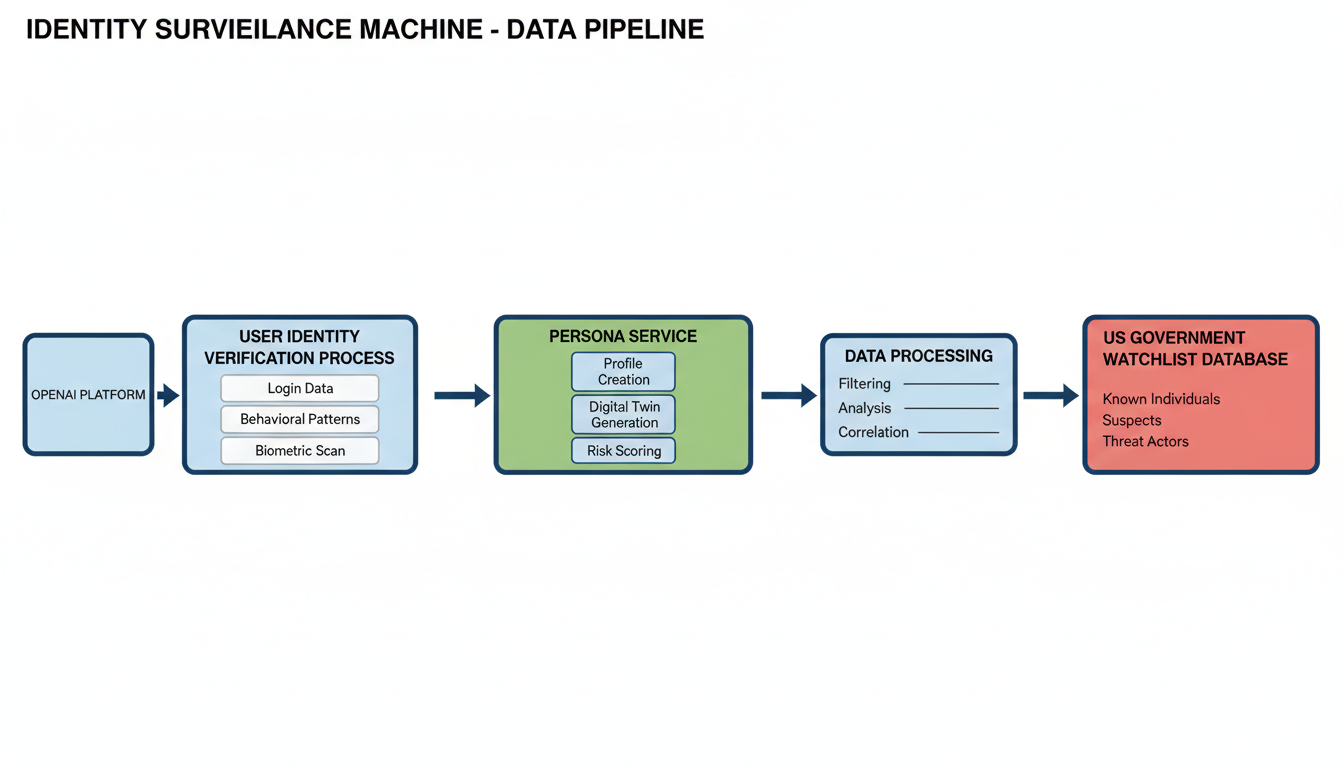
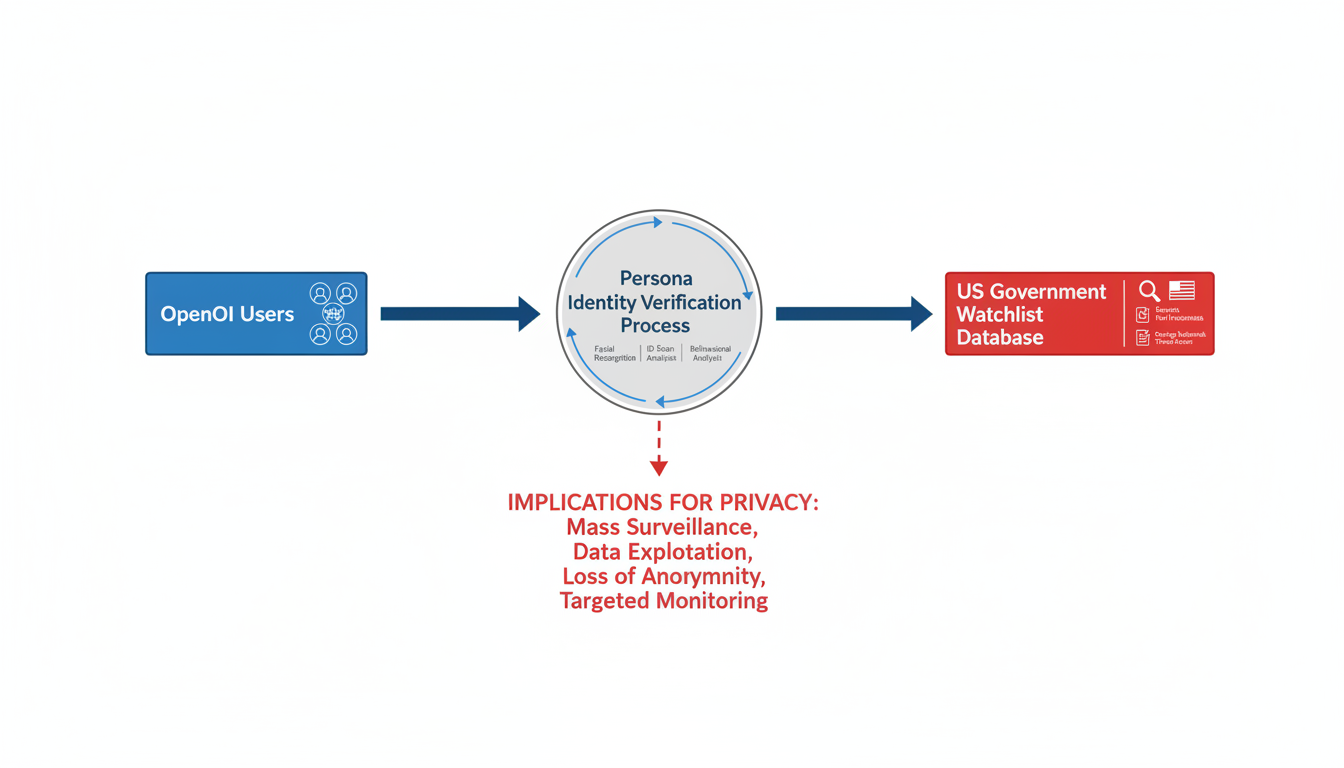
Recent allegations by security researchers vmfunc, MDL, and Dziurwa have brought to light claims of a sophisticated data pipeline, which they term an "identity surveillance machine," purportedly involving a collaboration between OpenAI, the identity verification service Persona, and the U.S. Government 1. This alleged system is said to process routine identity checks for OpenAI users and subsequently feed this sensitive data into a dedicated "watchlist" database 1.
The discovery of this alleged system stemmed from the finding of 53 megabytes of unminified TypeScript source maps. These files were reportedly found on a publicly accessible, FedRAMP-authorized government endpoint (app.onyx.withpersona-gov.com), enabling researchers to reconstruct the frontend codebase of Persona's government-facing dashboard 2. This report will delve into these claims, analyze their potential impacts, and explore what this means for individuals.
OpenAI's involvement in this alleged partnership is significant, as it has publicly mandated ID verification for its advanced models since mid-2025 2. Furthermore, mandatory Persona organization verification for access to GPT-5 was implemented in August 2025 2.
The Alleged System: Facts, Players, and Mechanisms
Security researchers vmfunc, MDL, and Dziurwa have alleged the existence of a sophisticated "identity surveillance machine" involving a data pipeline that links OpenAI, identity verification service Persona, and the U.S. Government 1. The discovery of this alleged system originated from 53 megabytes of unminified TypeScript source maps found on a publicly accessible, FedRAMP-authorized government endpoint (app.onyx.withpersona-gov.com) 2. These source maps allowed researchers to reconstruct the frontend codebase of Persona's government-facing dashboard 2.
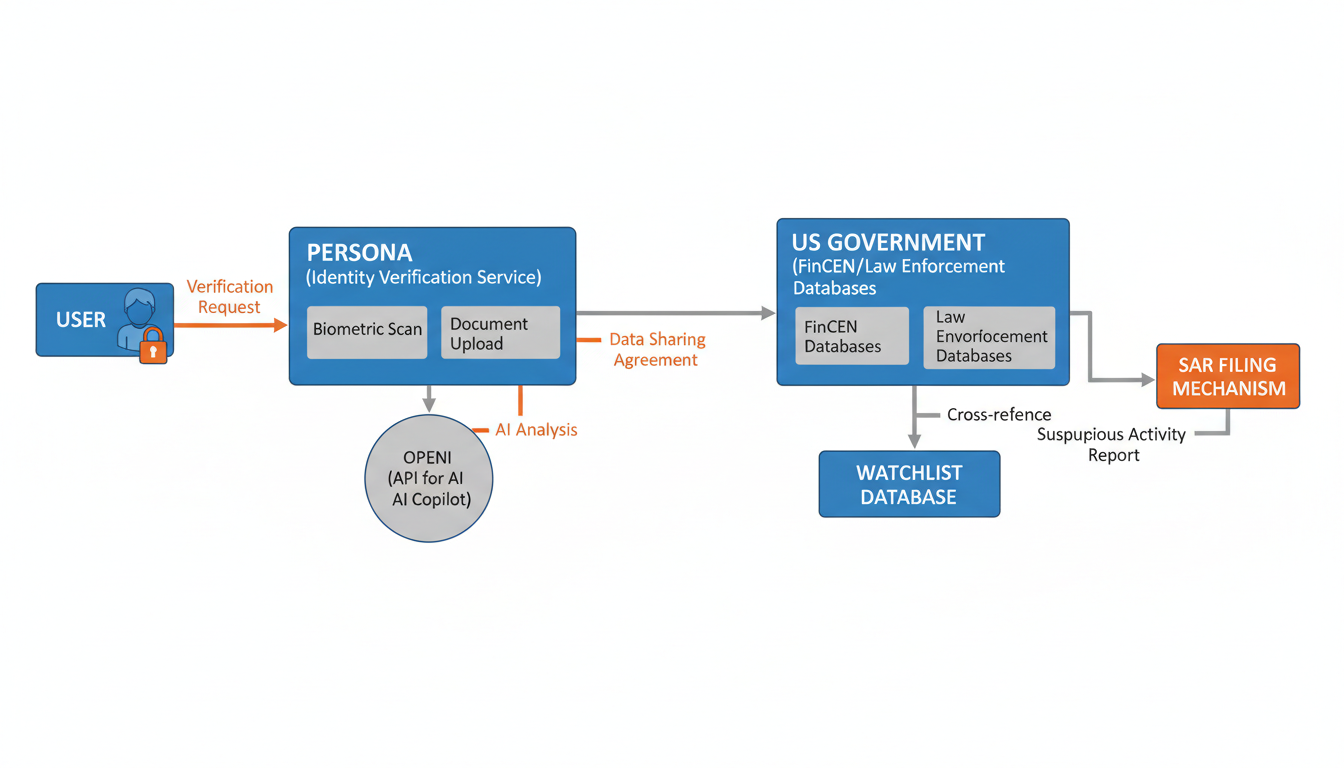
Persona Identities, Inc., founded in 2018, provides infrastructure for businesses to verify individuals and organizations, manage onboarding, and comply with Know Your Customer (KYC) and Anti-Money Laundering (AML) requirements 4. Persona employs various methods for identity verification, including document and biometric verification, proprietary selfie "liveness" checks, and database-based verification 4. Document verification involves collecting and verifying user information such as government IDs from over 200 countries and territories 5. Biometric verification utilizes facial geometries generated from government IDs and user-submitted selfies for 1:1 comparison 7. Proprietary selfie "liveness" checks determine whether a selfie or video belongs to a real, live person or is a spoof (e.g., mask, print, digital replay, AI-generated image, deepfake) 4. The system also supports NFC verification for passports with an NFC chip and conducts database checks 4. Persona states that facial geometries are immediately deleted after processing 8.
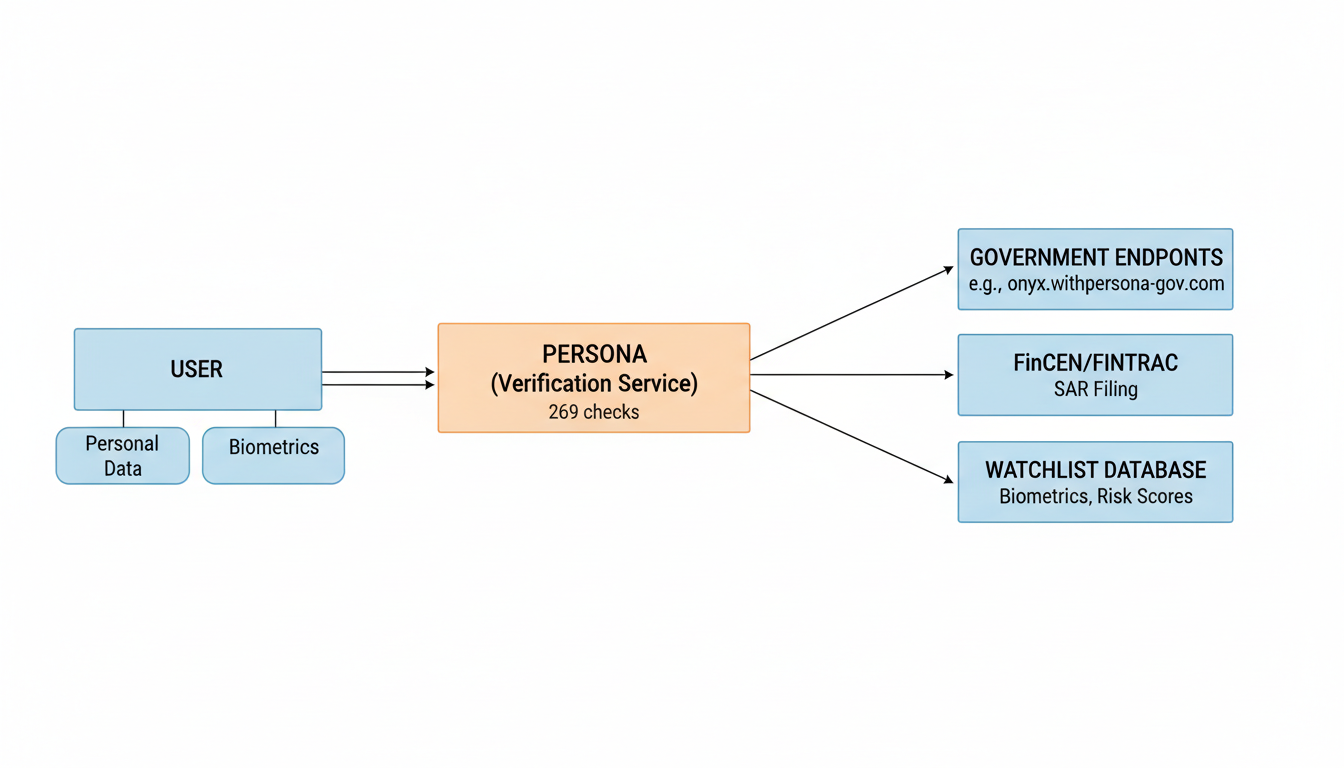
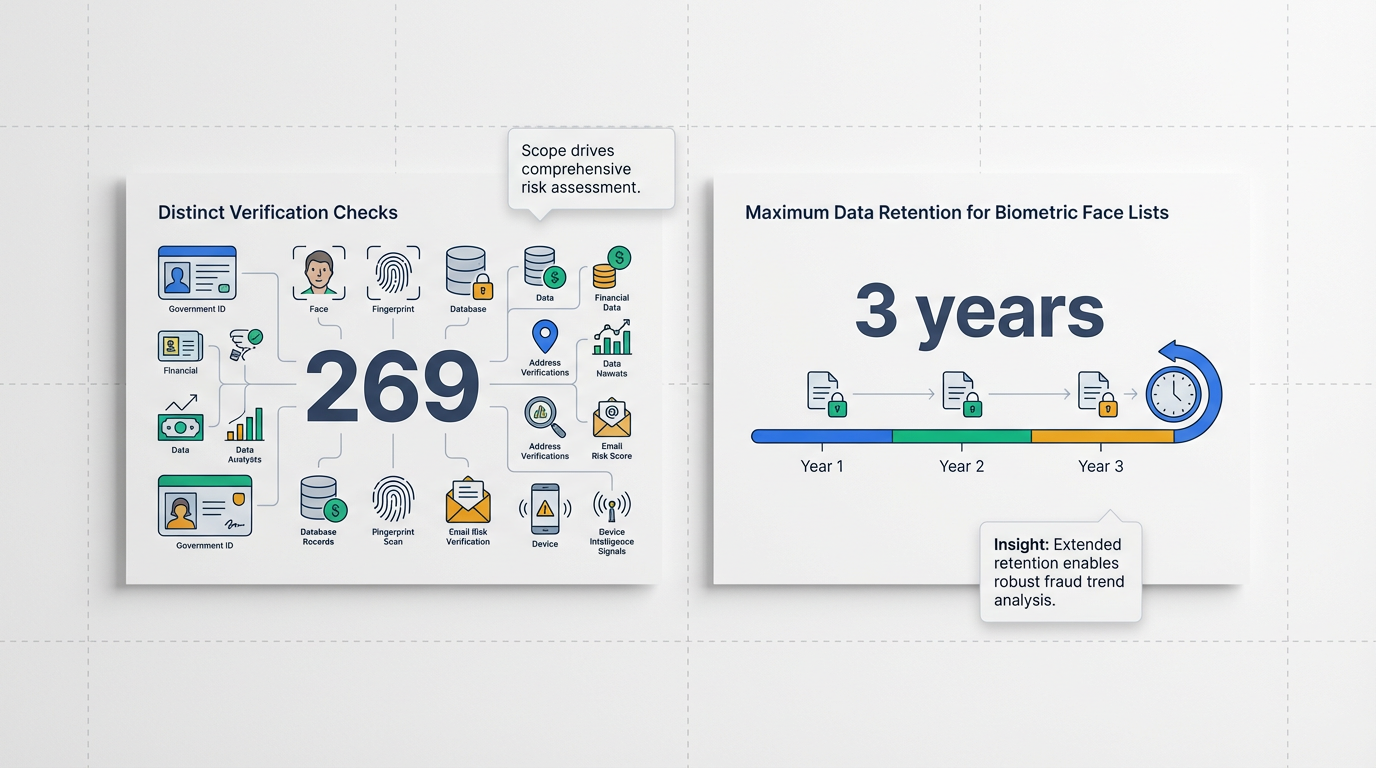
Despite Persona's stated focus on standard KYC/AML compliance, the exposed frontend code allegedly revealed capabilities far beyond routine identity verification 2. Researchers found that Persona's software performs 269 distinct verification checks 1. These checks reportedly include linking facial biometrics to financial records and law enforcement databases, screening against watchlists, and identifying "politically exposed persons" (PEP) 1. The system allegedly assigns "risk scores" based on facial similarity to watchlists and PEP status 2. Furthermore, it is claimed that the platform can screen for "adverse media" across 14 categories, such as terrorism or espionage 7.
Key alleged functions and capabilities revealed by the leaked code include:
| Alleged Function/Capability | Description |
|---|---|
| Suspicious Activity Reporting (SARs) | Includes a 'Send to FinCEN' button, allowing operators to file SARs directly to the U.S. Treasury's FinCEN and Canada's FINTRAC. |
| Biometric and Watchlist Screening | Links facial biometrics to financial/law enforcement databases, screens against watchlists and politically exposed person (PEP) status, maintains 'Face Lists' for 3 years, and assigns risk scores. |
| Intelligence Tagging | Can tag Canadian reports (STRs) and user data with codenames from active intelligence programs (e.g., Project ANTON, Project LEGION, Project SHADOW, Project ATHENA). |
| Crypto-wallet Tracking | Performs crypto-wallet tracking, including a native crypto address watchlist that persistently monitors flagged addresses via Chainalysis integration. |
| AI Copilot | An 'AskAI' feature, powered by OpenAI's API, reportedly assists government operators in reviewing dossiers and SARs in real-time. |
| Extensive Verification Checks | The leaked code revealed 269 distinct verification checks, far beyond simple age estimation. |
The code reportedly included a "Send to FinCEN" button, allowing operators to file Suspicious Activity Reports (SARs) directly with the U.S. Treasury's Financial Crimes Enforcement Network (FinCEN) 2. Similarly, capabilities for filing reports with Canada's FINTRAC were identified 15. The system also allows for tagging user data with specific public-private intelligence program codenames, such as "Project ANTON," "Project LEGION," and "Project SHADOW," and "Project ATHENA" 2. Allegations further suggest crypto-wallet tracking, including a native crypto address watchlist that persistently monitors flagged addresses via Chainalysis integration 1. The system reportedly maintains "Face Lists" with a 3-year retention policy for recurring screening of users 2, though Persona CEO Rick Song explicitly denied that Persona links facial biometrics to financial records or law enforcement databases for any customer 1.
OpenAI's alleged involvement stems from its requirement for ID verification for advanced models since mid-2025 and mandatory Persona organization verification for GPT-5 access in August 2025 2. The leaked code also reportedly revealed an "AskAI" feature, powered by OpenAI's API, designed to assist government operators in reviewing dossiers and SARs in real-time 2. OpenAI's stated goals for implementing such verification include preventing malicious use, blocking state-backed attackers, preventing intellectual property theft, meeting regulatory compliance, and managing capacity for its advanced AI models 3.
The U.S. Government's role is implicated through the FedRAMP authorization of the endpoint where the source maps were discovered, app.onyx.withpersona-gov.com 2. This suggests a dedicated federal surveillance-linked instance 2. Additionally, the subdomain openai-watchlistdb.withpersona.com was identified as a dedicated Google Cloud instance operational since November 2023, indicating infrastructure specifically tailored for high-stakes federal data, which researchers argued exceeded standard age verification needs 2. While Persona CEO Rick Song stated the company does not currently work with any federal agency for user surveillance, he acknowledged pursuing FedRAMP authorization for workforce security 16.
Persona prioritizes data security and privacy, claiming a "security and privacy first approach" 6. The company states it is GDPR and CCPA compliant 18, and holds certifications including SOC 2 Type II, ISO 27001, and FedRAMP Authorized at the Low Impact level 18. Data protection measures include AES-256 encryption for data at rest, HTTPS with TLS 1.2 or higher for data in transit, strict access controls based on the principle of least privilege, and regular third-party penetration testing 21. Persona also states it does not sell user data and provides tools for data control and deletion 18. However, researchers have characterized the publicly exposed frontend on a FedRAMP-authorized platform as a "serious security failure" 7, contrasting with Persona's claims of robust security. Concerns were also raised about Persona's data retention policies, with internal code leaks suggesting retention of biometric face lists for up to three years 2, conflicting with some partner privacy policies 15.
Potential Impacts: Erosion of Privacy and Civil Liberties
The alleged "identity surveillance machine" collaboration between OpenAI, Persona, and the U.S. Government, as described by security researchers, poses significant threats to individual privacy and civil liberties. The extensive capabilities revealed in the leaked code highlight a potential for the broad erosion of fundamental rights through sophisticated data collection, retention, and access mechanisms.
The system's broad scope of data collection is a primary concern. Persona's software reportedly performs 269 distinct verification checks, a number far exceeding what most users would expect for routine identity verification 7. These checks include facial recognition against watchlists and politically exposed persons (PEP), screening "adverse media" across 14 categories (e.g., terrorism, espionage), and assigning risk and similarity scores 7. This extensive collection of biometric and personal data creates a comprehensive digital profile for individuals.
Compounding the issue are the extensive data retention policies. While Persona states that facial geometries are immediately deleted after processing, internal code leaks suggested that biometric face lists can be retained for up to three years 8. This means that data such as IP addresses, browser and device fingerprints, government ID numbers, phone numbers, names, faces, and selfie analytics could be retained for an extended period, leading to persistent surveillance 7. Such long-term retention policies raise alarms about potential misuse and conflict with standard privacy expectations 15.
The risk of government overreach is substantial, with capabilities such as direct filing of Suspicious Activity Reports (SARs) to the U.S. Treasury's Financial Crimes Enforcement Network (FinCEN) and its Canadian equivalent, FINTRAC 15. The platform also allegedly allows tagging user data with specific public-private intelligence program codenames like "Project SHADOW," "Project ANTON," and "Project ATHENA" 15. The existence of a dedicated government-facing instance (onyx.withpersona-gov.com) and a "watchlist" database (openai-watchlistdb.withpersona.com) suggests a direct pipeline for government access and use of personal data beyond standard financial intelligence 2.
This linking of facial biometrics to financial and law enforcement databases, combined with continuous watchlist screening, poses a severe threat to individual privacy 1. The system's ability to assign "risk scores" based on facial similarity to watchlists and "politically exposed person" status raises significant civil liberties concerns 2. Such algorithmic assessments can lead to bias, discrimination, and a chilling effect on free expression, as individuals may self-censor knowing their activities are subject to such scrutiny 16. Privacy advocates have voiced unease about the potential for data obtained during routine verification checks to be used for mass surveillance or shared with foreign governments 4.
The phenomenon of "function creep" is evident, where identity verification, initially intended for simple age or identity checks, has allegedly transformed into a sophisticated "full-service financial intelligence terminal" 2. This blurs the lines between essential security measures and pervasive surveillance, eroding public trust and individual autonomy 1. The shift from verifying identity to monitoring individuals for financial crime and intelligence purposes represents a significant expansion of power without explicit public consent or robust oversight.
Finally, the public exposure of 53 megabytes of unminified TypeScript source maps on a FedRAMP-authorized government endpoint highlights serious data security risks 2. Despite Persona's stated commitment to data security and certifications like SOC 2 Type II and ISO 27001 18, this incident demonstrates potential vulnerabilities that could expose sensitive user data to unauthorized access. Security researchers noted this as a "serious security failure" for a FedRAMP-authorized platform 20.
What Ordinary People Can Do: Awareness and Action
To protect digital identity and privacy against surveillance systems, particularly those involving identity verification services and government data collection, individuals can take proactive steps. This includes managing personal data, adopting secure practices, understanding their rights, and actively advocating for stronger privacy protections.
Protecting Personal Data in Online Services and Identity Verification
When you use online services, especially those asking for identity verification, it's crucial to manage your data carefully:
- Data Minimization and Control: Look for and support systems that only collect the data absolutely needed for a service 25. You should advocate for transparency in how your data is created, used, and kept, and demand control over what information you share 25. Tools like Mobile Digital IDs (mDLs) and digital wallets can help you share only specific information, like your age, without revealing everything 27. However, current mDL standards need stronger privacy features to prevent data leaks 25.
- Opt for Physical Alternatives: Whenever possible, you should have the choice to use physical documents instead of digital ones, as digital systems can come with risks like surveillance and data misuse 25.
- Scrutinize Online Sharing: Be careful about what you share publicly online, including on social media and websites. Try searching your own name, address, or phone number on Google to see what's visible to others 29. You can use services like DeleteMe or TallPoppy to opt out of data broker registries, but the best approach is to limit what you share in the first place 29. Always set your social media accounts to private, limit visible profile information, and consider using different screen names or accounts for personal and professional use 29. Before sharing photos, make sure to remove any location information (metadata) from them 29.
Tools and Practices for Enhancing Digital Security and Anonymity
Experts suggest using multiple layers of security to protect yourself online:
- Encryption: Use communication apps like Signal or Proton Mail that offer end-to-end encryption for sending sensitive messages 29. Also, ensure your devices have full-disk encryption turned on, which protects your data even if your phone or computer is lost or stolen; this feature is available on iOS and Android devices 29. Encryption scrambles your data, making it unreadable without the right key 29.
- Strong Passwords and Multi-Factor Authentication (MFA): Create unique, complex passwords that mix letters, numbers, and symbols, and update them regularly. Avoid using the same password for different accounts 29. Password managers can help you create and store these strong passwords, meaning you only need to remember one master password (though be aware they can be a single point of failure if compromised) 29. Always turn on Multi-Factor Authentication (MFA) or 2FA for your accounts; using code generator apps or hardware tokens is more secure than receiving codes via SMS or email 29.
- Privacy-Focused Browsing: Use web browsers like Firefox and search engines like DuckDuckGo that are designed not to track your online activities 29. Organizations like the Electronic Frontier Foundation (EFF) offer tools such as Privacy Badger, Surveillance Self-Defense, Certbot, Cover Your Tracks, and Atlas of Surveillance to help you protect your privacy 25.
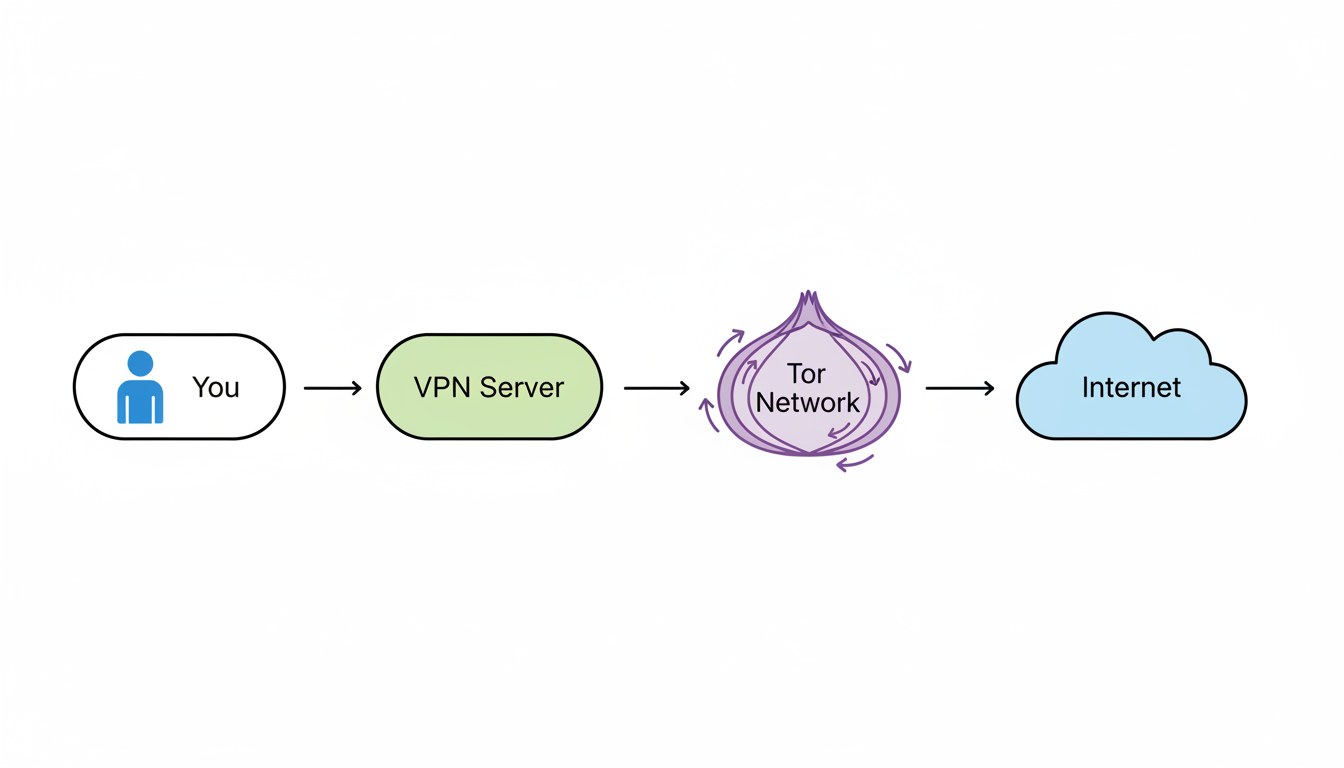
- Virtual Private Networks (VPNs): A VPN encrypts your internet connection and helps reduce tracking, which is especially important when using public Wi-Fi 29. For extra anonymity, particularly when using the Tor network, it's recommended to connect through a trusted VPN first (You → VPN → Tor → Internet). This setup helps hide your use of Tor from your Internet Service Provider (ISP) and adds an extra layer of protection against being identified 30.
- Tor Network: The Tor network (The Onion Router) is a system that sends your internet traffic through many volunteer-run servers worldwide, encrypting it in layers, much like an onion 30. This makes it very difficult to trace your location and online activities, boosting your privacy 30. Tor is especially useful for bypassing censorship and protecting communications for activists and journalists 31.
- Using Tor Safely: Always download Tor Browser directly from the official Tor Project website 33. Keep your operating system and Tor Browser updated 33. Avoid logging into personal accounts (like social media or email) while using Tor, as this can compromise your anonymity 33. Disable any browser plugins or add-ons in Tor Browser, as they might reveal your IP address 33.
- Limitations of Tor: While powerful, Tor has drawbacks. Your browsing speeds might be slower, some websites may block Tor users, and it's not entirely foolproof 31. The "exit nodes" (the last server before your traffic leaves the Tor network) can be monitored, potentially exposing unencrypted data if the website you visit doesn't use HTTPS 33. Tor's security can also be limited against well-funded attackers 35. It's not a "free VPN," as malicious Tor exit nodes can downgrade HTTPS or tamper with downloads 30.
Advocating for Stronger Digital Rights and Privacy Protections
You can actively contribute to improving digital rights and privacy:
- Educate and Inform: Stay informed about privacy issues by consulting reliable sources such as the International Association of Privacy Professionals, The Hacker News, Privacy International, WIRED, and the EFF's Surveillance Self-Defense toolkit 29. Share this knowledge with your friends and family to help them protect their privacy too 36.
- Engage with Lawmakers: Contact your local and state representatives to discuss your privacy concerns and ask about their stance on digital rights 36. Inquire if your city council has a committee for data privacy, or suggest forming one and advocating for citizen positions 36.
- Form Community Coalitions: Join or create local advocacy groups, similar to those under the Electronic Frontier Association, to educate officials on data policies and threats, and inform the public through talks 36.
- Support Legislation: Advocate for strong federal privacy laws that recognize privacy as a basic right 37. Support initiatives like the EFF's "My Body, My Data Act" to protect sensitive personal information 36.
- Advocate for "Privacy-First" Policies: Support policies that tackle online harms by prioritizing privacy, such as banning surveillance-based behavioral advertising or requiring true opt-in consent for data collection 26. This approach can help protect children, support journalism, safeguard health data, promote digital justice, ease concerns about AI, and counter surveillance from foreign governments 26.
- Oppose Harmful Digital ID Schemes: The EFF strongly opposes mandatory national ID systems and age verification that limits access to free web content 25. Advocacy should push for mandatory privacy guidelines in digital ID systems, rather than just suggestions 25.
Key Digital Rights to Understand
It's important for everyone to know about several core digital rights that are at risk from surveillance and data collection:
- The Right to Privacy: The Fourth Amendment of the US Constitution protects against "unreasonable searches and seizures," generally requiring warrants for the government to access personal information 38. However, law enforcement agencies are increasingly buying personal data (like location or facial recognition data) from private data brokers, bypassing the need for traditional court oversight 38. This practice fundamentally shifts the balance between national security and individual privacy, as the vast amount of data collected by private companies can reveal very sensitive information about your health, finances, race, and more 38.
- Protection Against Discrimination: Digital data collection and the algorithms used to process it can worsen existing social inequalities, leading to discrimination in areas such as employment, housing, healthcare, and voting rights, especially for marginalized communities 25. Algorithms can unintentionally carry historical biases, resulting in "digital redlining," where certain groups receive disadvantageous offers or are excluded from opportunities 40.
- Freedom of Expression: Extensive digital surveillance can make people afraid to express themselves online, leading to self-censorship or avoidance of political expression due to fears of being monitored or punished 41. This is known as a "chilling effect" on First Amendment rights.
- Data Minimization, Transparency, and User Control: Any digital identity system should be built on key principles: collecting only necessary data, being clear about how data is used and kept, and giving users control over what they share 25. These principles are vital to prevent your personal information from being misused.
- Right to Choice and Opt-Out: Digital services, particularly those offered by the government, should be optional, with physical alternatives available 25. You should always have the ability to opt-out of data collection and targeted advertising.
Conclusion: A Call for Vigilance in the Digital Age
The allegations of an "identity surveillance machine" involving OpenAI, Persona, and the U.S. Government, brought to light by security researchers vmfunc, MDL, and Dziurwa, underscore a critical juncture in the balance between technological advancement and fundamental human rights. This alleged system, uncovered through 53 megabytes of unminified TypeScript source maps on a publicly accessible government endpoint, reportedly functions as a sophisticated data pipeline for routine identity checks that feeds into a dedicated "watchlist" database 1. OpenAI's implementation of mandatory Persona verification for advanced models since mid-2025 further highlights the centrality of identity verification in the AI ecosystem 2. While Persona's CEO has denied specific claims about linking facial biometrics to financial or law enforcement databases and clarified intelligence codenames, the technical credibility of the research has been noted by some experts 1. OpenAI, for its part, has not issued a formal response to these specific allegations 16.
The potential capabilities revealed in the leaked code, such as a "Send to FinCEN" button for Suspicious Activity Reports (SARs), biometric and watchlist screening, crypto-wallet tracking, and an "AskAI" feature for government operators, portray Persona's platform as far more extensive than standard identity verification 2. The system reportedly conducts 269 distinct verification checks, encompassing facial recognition against watchlists and politically exposed persons (PEP), and assigns "risk scores" 1. Such pervasive capabilities pose profound threats to privacy, civil liberties, and fundamental freedoms, representing a concerning "function creep" from identity verification to broad surveillance 1. The controversy has already seen Discord cut ties with Persona, citing data practices and surveillance allegations 43. The involvement of investors like Founders Fund, backed by Peter Thiel, further fuels concerns given Thiel's historical ties to government surveillance programs 43. The ongoing litigation against Persona under the Illinois Biometric Information Privacy Act (BIPA) also underscores public and legal concerns regarding biometric data collection without proper consent 20.
In the face of these evolving surveillance technologies, continuous public discourse, individual vigilance, and proactive measures are critically important. Citizens must advocate for stronger digital rights, robust privacy protections, and demand greater transparency from both corporations and governments regarding data collection and usage 25. Practical steps for individuals include adopting data minimization practices, opting for physical alternatives over digital whenever possible, and carefully scrutinizing online information sharing 25. Furthermore, enhancing personal digital security through encryption, strong passwords, multi-factor authentication, privacy-focused browsing, and the strategic use of VPNs and the Tor Network can bolster individual anonymity and data protection 29.
Ultimately, the preservation of rights such as the right to privacy, protection against discrimination, and freedom of expression hinges on an informed and active citizenry 25. As digital identity systems become increasingly integrated into daily life, it is imperative to push for systems that uphold data minimization, transparency, user control, and the fundamental right to choice and opt-out 25. Only through collective awareness and concerted advocacy can we safeguard our digital identities and fundamental freedoms against the encroaching shadows of surveillance.